First Day of School
By Duncan Sparrell, sFractal Consulting, OASIS Open Board Member

There’s a great scene at the end of Steven Spielberg’s extraterrestrial opus Close Encounters of the Third Kind (apologies: spoilers ahead), in which a team of human scientists initiate a dialogue with an alien ship via an amplified synthesizer and a board of lights. Two entirely different species bark and bellow at one another in sharp figures and dancing lights that no one seems to fully understand.
“It seems they’re trying to teach us a basic tonal vocabulary,” one of the scientists says.
Another guy offers simply, “It’s the first day of school, fellows.”
Sound familiar? Anyone who has ever tried to bridge the technical side of cybersecurity in a discussion with the business community might be able to relate to the conundrum of two wildly different groups trying desperately to speak one another’s language.
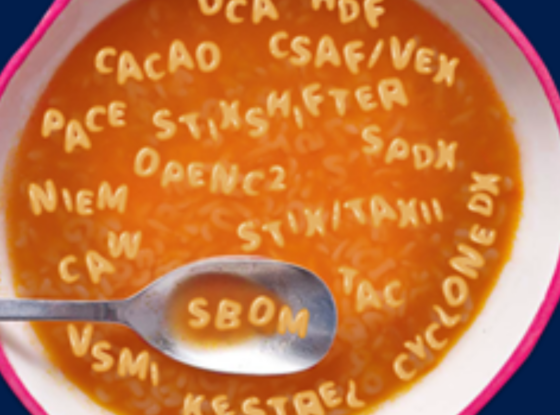
In the case of the Close Encounters parable, it’s worth entertaining the idea that you and I and everyone else working to standardize cybersecurity automation may be the aliens. Don’t believe me? Try saying this to a loved one over dinner: “CASP, STIX/TAXII, CACAO, OCA, PACE, CVE, SBOM, VEX, IOB, TAC, NIEM, STIX Shifter, Kestrel, OpenC2, OCSF, OXA, VSMI.”
Those of us who have devoted years of our professional lives to advancing cybersecurity automation are in the unfortunate position of imparting vital technical knowledge to essential stakeholders who may not speak our language.
The 2023 National Cybersecurity Strategy spells it out in no uncertain terms: “By working in partnership with industry; civil society; and State, local, Tribal, and territorial governments, we will rebalance the responsibility for cybersecurity to be more effective and more equitable.”
Put another way, it is now incumbent on the various tribes of cybersecurity stakeholders to pool their ideas and unite their efforts to build upon a shared vernacular.
The Need for Common Language
Divergent perspectives, objectives, and bodies of knowledge must be knit together. Our effectiveness and resilience as cybersecurity professionals depends on our ability to braid common truths, shared goals, and universal language together into a structural network of agreed upon practices and products that shield our digital world.
President Biden’s Executive Order 14028 gives a pithy cybersecurity principle for the macro level: “In the end, the trust we place in our digital infrastructure should be proportional to how trustworthy and transparent that infrastructure is, and to the consequences we will incur if that trust is misplaced.“
But the devil is in the details – and each tribe tends to dive into its own details which are incomprehensible to the other.
We’re back at the moment of musical contact in Close Encounters. Two of the most intrepid, visionary, and extremely capable communities can remain aloof behind privileged expertise. Or, we can step out of our respective domains of knowledge and make a concerted effort to see how the other half lives.
Technically-minded wizards of the cybersecurity world must go to great lengths to communicate our work in a way that retains its value without obstructing it within a veil of the obtuse. Metaphor, allusion, and analogy, though slippery, are powerful tools that can help us bridge immense divides. Even closer to home, we do well to unbury our heads from silos of specialization and cultivate a broader grasp of what our colleagues are proposing, testing, and adopting.
Big pictures painted in the language of broad strokes are not the only art we need to fine-hone. Sometimes simple business numbers do more to influence acquisition and implementation of cybersecurity technology than any dazzling technical brief could. I am confident that cybersecurity automation is a no-brainer cost/risk reduction if we just did the math and converted the sum to dollars. After all, wise expenditures are just good business and financial quantification is an almost monolithically important aspect of business decision making.
We Should Be Good at Influencing Industry With Quantified Risk Projections, but Somehow We Aren’t
When a new exploit or a staggering zero-day lurks around every corner, prognosticating on the future with anything approaching certainty feels like a foolish way to end up appearing short-sighted. Accordingly, we need to accustom ourselves to operating in a window of probabilities. “Could,” “might,” and “maybe” are powerful words when coupled with rate of response and financial liability figures.
Hubbard & Seiersen’s cybersecurity Rosetta Stone for stakeholder communication takes inspiration from the exact other end of the cinematic universe as Close Encounters. Their approach borrows from the straightforward sports agent jargon of Jerry Maguire–cut the excuses and show them the money. A particularly sharp rhetorical buzzsaw from “How to Measure Anything in Cybersecurity Risk” lays it all out: “there are plenty of fields with massive risk, minimal data, and profoundly chaotic actors that are regularly modeled using traditional mathematical methods.” What’s our excuse?
The Stakes Couldn’t Be Higher
Critical systems are woefully vulnerable even though we have the ability to reduce this risk. The Johns Hopkins University Applied Physics Lab produced a study on cybersecurity that produced stunning results. Properly deployed cybersecurity automation can limit the scope of an exploit from weeks to minutes reducing damage by several orders of magnitude.
These numbers and the technology that produced them are only as valuable as our ability to communicate them. Without initiating a dialogue that challenges us to learn new modes of conversation, we risk remaining alien to one another and losing mightily in our potential to grow in support of one another.
For myself and many of my colleagues who have spent their entire careers grappling with huge challenges in the field of cybersecurity, it’s not the first day of school. Far from it. But we live in exciting times with unanticipated sea changes that require fresh thinking. I think we are up to the challenge if we work together and I couldn’t be more excited to embark on this journey with all of you to translate the alphabet soup of cybersecurity automation into quantitative business risk reduction.